the Wrong Stuff
 ⌘ Read more
⌘ Read more
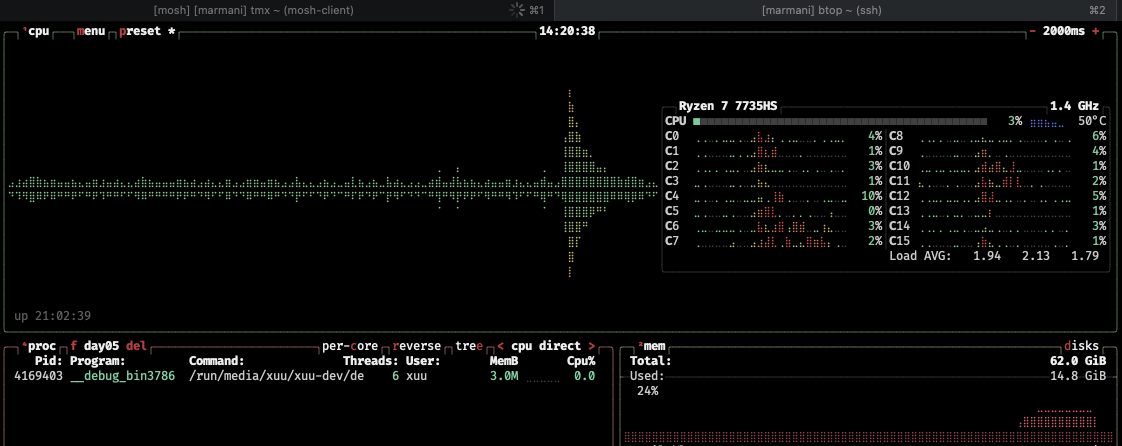
Its the latest ryzen 7 chipset for laptop/mini form factor.
I am very surprised about the times others are getting. I guess that’s the difference between interpreted and compiled showing.
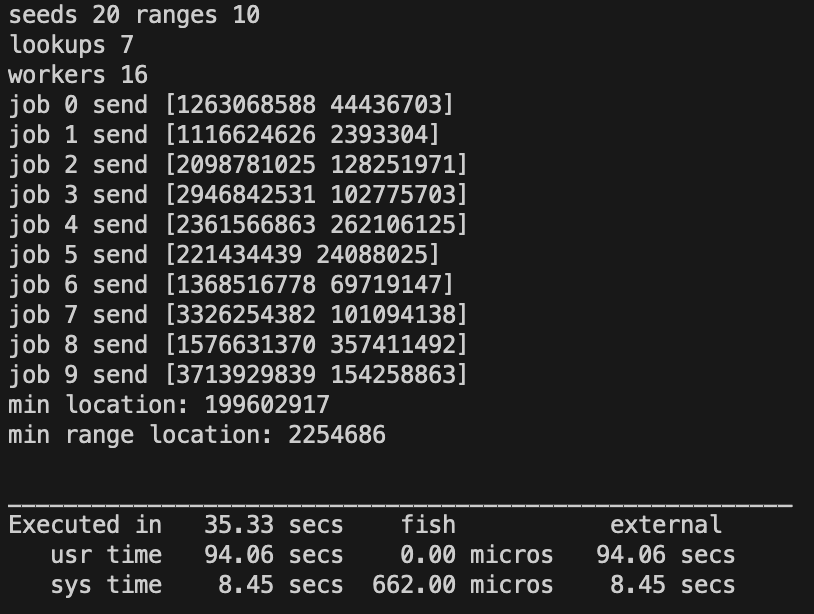
took a few attempts.. but i managed to do it in half the time!
@movq@www.uninformativ.de It took a little over a minute on my machine.. i should try to make it multi threaded.. 🤔
Executed in 68.96 secs fish external
usr time 60.84 secs 242.00 micros 60.84 secs
sys time 12.52 secs 252.00 micros 12.52 secs
With all M$’s apps being basically fancy web apps, there is no need to actually install any of their legacy applications locally anymore. Since I am online basically 100% of the time this turns my Office experience in a Chromebook like one. No installs, never outdated software. Just a yearly subscription contribution to worry about.
… it just finished and brute-force worked. 18 minutes of computing time on my 11 year old machine, single-threaded.
My son said for the first time he wanted to make a game himself today. Going to freshen up my canvas and collision detection skills.
I would love to be able to time travel back to the days when Talking Heads toured and witness one of their epic live concerts.
Hey Apple, it’s 2023 - about time to start supporting the content indexation of markdown files in Spotlight out of the box, don’t you think?
@xuu@txt.sour.is Ah, you went with the “scanning” approach as well. I did that, too.
It’s quite surprising to see (imho) how many people on reddit started substituting strings (one becomes 1 etc.). That makes the puzzle much harder by introducing nasty corner cases.
(Maybe I was just lucky this time to pick the correct approach right from the start. 🤣 Or maybe it’s a bit of experience from doing past AoC events …)
Went to the Christmas market for the first time this year.
Feeling nostalgia for simpler web development times.
Context-switches are a real productivity killer if it means that by the time you get back to the previous context your remote desktop session expired.
The best gift anyone could give me is the time to be able to finish reading some books.
Pinellas County - 90’: 9.10 miles, 00:09:28 average pace, 01:26:06 duration
brrrr…. pretty decent run. thought the HR would creep more with how much i was wearing. only stopped five times to hack up a lung.
#running
Full moon tonight: time to play #nethack :)
It is that time of year where I try to be extra nice in customer service Quality and feedback surveys. I once worked on the other side of these, so it might brighten someone’s day.
Oceanography Gift
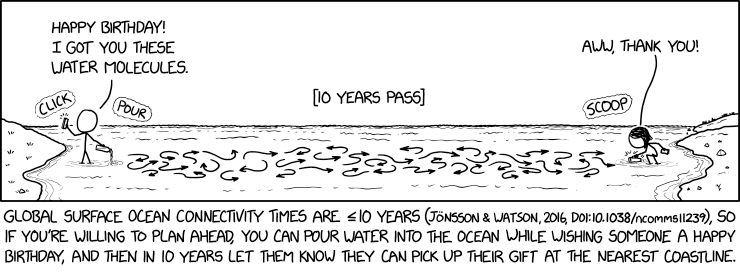 ⌘ Read more
⌘ Read more
There is a lot of Black Friday promotion happening in Germany these days - I wonder however how many Germans really know where it comes from? Happy Thanksgiving to whoever is celebrating today - as it is one of the few US / Canadian festive days where families - really - try to enjoy their time together.
First time ever I made something that uses Redis
@prologic@twtxt.net its not.. There are going to be 1000s of copy cat apps built on AI. And they will all die out when the companies that have the AI platforms copy them. It happened all the time with windows and mac os. And iphone.. Like flashlight and sound recorder apps.
@prologic@twtxt.net the new product was GPTs. A way to create tailored bots for specific use cases. https://openai.com/blog/introducing-gpts (fun fact: I did an internal hackathon where we made something like this for $work onboarding. And I won a prize!)
The competed project is poe https://quorablog.quora.com/Introducing-creator-monetization-for-Poe which is basically the same idea. Make a AI bot tailored to a specific domain of knowledge. And monitize it.
The timing fits very well as openAI announced it just a few weeks ago.
@movq@www.uninformativ.de I lasted for a long time.. Not sure where or when it was “got”. We had been having a cold go around with the kiddos for about a week when the wife started getting sicker than normal. Did a test and she was positive. We tested the rest of the fam and got nothing. Till about 2 days later and myself and the others were positive. It largely hasn’t been too bad a little feaver and stuffy noses.
But whatever it was that hit a few days ago was horrible. Like whatever switch in my head that goes to sleep mode was shut off. I would lay down and even though I felt sleepy, I couldn’t actually go to sleep. The anxiety hit soon after and I was just awake with no relief. And it persisted that way for three nights. I got some meds from the clinic that seemed to finally get me to sleep.
Now the morning after I realized for all that time a part of me was missing. I would close my eyes and it would just go dark. No imagination, no pictures, nothing. Normally I can visualize things as I read or think about stuff.. But for the last few days it was just nothing. The waking up to it was quite shocking.
Though its just the first night.. I guess I’ll have to see if it persists. 🤞
Pinellas County - 5 mile progression: 5.01 miles, 00:09:00 average pace, 00:45:10 duration
was hoping for a rain, mist, or whatever but alas it did not happen. comfy run and talked with several people in the park. exchanged pleasantries with the older gentleman i see all the time. had to run in the grass towards the end for some kids on bikes who never passed me. must have been going fast!
#running
Hey Apple, it’s 2023 - about time to start supporting the content indexation of markdown files in Spotlight out of the box, don’t you think?
DeepMind AI can beat the best weather forecasts - but there is a catch
By using artificial intelligence to spot patterns in weather data, Google DeepMind says it can beat existing weather forecasts up to 99.7 per cent of the time, but data issues mean the approach is limited for now ⌘ Read more
@movq@www.uninformativ.de time to write your own browser? Or at least a fork maintained outside the EU?
time to tackle all that clutter
Come on! how do I keep my pet next to me in #nethack? They always go wandering without me and I loose them or my time trying to find them
Anyone have any ideas how you might identify processes (pids) on Linux machine that are responsible for most of the Disk I/O on that machine and subsequently causing high I/O wait times for other processes? 🤔
Important bit: The machine has no access to the internet, there are hardly any standard tools on it, etc. So I have to get something to it “air gapped”. I have terminal access to it, so I can do interesting things like, base64 encode a static binary to my clipboard and paste it to a file, then base64 decode it and execute. That’s about the only mechanisms I have.
I’ll shut down this instance soon, I want to say thanks to all of you, especially @prologic@twtxt.net . It’s been fun here, but I do not spend much time here anymore - cutting down on the things I host and use \ spend time on etc.
I’ve been using activitypub more - since it’s more or less replaced ‘x’ for me, and can be reached at:
@stigatle@activitypub.stigatle.no
Pinellas County - Base: 7.25 miles, 00:10:21 average pace, 01:15:03 duration
it was alright. had to wait too long each time i crossed 113th, the second time the blood rushed to my head and made me a bit nauseous so walked that off.
#running
More data contradicting the existence of “echo chambers”. As I’ve argued many times before, the concept of an echo chamber or information bubble is not real. The podcast below is an interview of an author of a study where they actually intervened and changed the information diet of 20,000 people (with consent!), then surveyed them after three months. They observed essentially no changes to the study subjects’ beliefs and attitudes. They also observed that the typical person, while they tend to gravitate towards people with similar political leanings, only get about 50% of their content from such like-minded people. They get the rest from neutral sources and maybe 20% from non-like-minded people.
Varied information diet + No change in attitudes when information diet is forced to be different = no echo chamber.
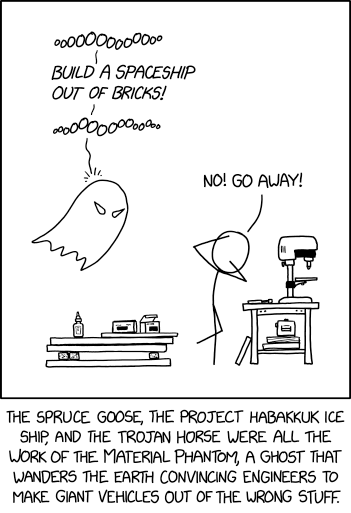
Haunted House
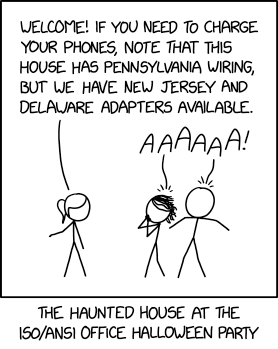 ⌘ Read more
⌘ Read more
Time to write my own S3-compatible Object Storage server 🤣
I think about 8pm is the ideal time for sunset.
@prologic@twtxt.net yeah, it’s true. Thing is, Linux as a desktop operating system sucked in 1996 yet I adopted it then anyway because I wanted nothing to do with MS anymore 😆 I know it’s not for everyone but I’m pretty tolerant of a less-than-stellar experience if it means I can be free of big-company garbage.
I haven’t tried a Linux-based smartphone OS in a long time so I don’t have any idea how bad/good it might be. I figure when I finally break down and get a new phone I’ll experiment on my current phone.
@adi@twtxt.net @prologic@twtxt.net F-droid. Getting APKs from developers you trust and side-loading them. Some flavor of Linux. Some distro of the open source parts of Android.
There are lots of options. Bit by bit I divest from anything that’s distributed from Google Play. With my latest phone I find and download APKs so that I could have the app without all the Google crap woven through it. By the time I need to replace this one I’ll be fully free of Google Play. Most of my apps come from F-droid now. You can a perfectly functional phone/pocket computer unless you’re addicted to installing dozens of corporate apps.
@jmjl@tilde.green I’m sorry that I’m not super knowledgeable about alternatives to jmp.chat but I’ll tell you what I know.
You’re probably right about jmp.chat not working for you, at least as it is now. You can only get US and Canadian phone numbers through it last time I checked, so if you’re not in either of those countries you’d be making international calls all the time and people who wanted to call you would be making international calls too.
I’ve seen people talk about using SIP as an intermediary: you can bridge SIP-to-XMPP, and bridge SIP-to-PSTN (PSTN = “packet switched telephone network”, meaning normal telephone). You can skip the SIP-to-XMPP side if you’re comfortable using a SIP client. I don’t know very much about SIP or PSTN so I am not sure what to recommend, but perhaps this helps your search queries.
There are a fair number of services like TextNow that let you sign up for a real telephone number that you can then use via their app (I wouldn’t use TextNow–they had tons of spyware in their app). I don’t know if that kind of service works for you but if it does perhaps you’d be able to find one of them that isn’t horrible. This page (https://alternativeto.net/software/jmp-chat/) has a bunch of alternatives; I can’t vouch for any of them but maybe it’s a starting point if you want to go this route.
Good luck!
@mckinley@twtxt.net Yes, I’m still with jmp.chat, and still very happy with them overall. Their beta period ended and their pricing increased a bit, so that’s worth a bit of consideration. I also managed to get one of their eSIMs. I’m slightly less happy with that aspect of their service, though they seem to be actively working on improving it and I knew in advance this was an early beta kind of thing and likely to have issues.
The only unreliability with calls that I’ve noticed was traceable to the unreliability of my own internet connection. I’ve confused incoming calls by simultaneously making and taking calls from the computer and the phone, but I think it’s understandable that problems might arise and that’s not a real use case for me. Once or twice I did not receive a text transcription of a voice mail, but the support is usually quick to address things like that.
I host my own XMPP server and have for a good decade now, and that’s what I use with jmp.chat. I can’t speak to the quality of their hosting options.
Group texting works fine for me if one of the other parties initiates the group text. I haven’t tried to initiate my own group text in well over a year; last time I did, it didn’t work. That may or may not be a problem for you, and it may or may not have been fixed by now. Worth investigating more if it’s important. I should also say I’ve only ever used group texts with 3 participants, and can’t speak to what happens if there are more nor whether there are upper limits.
Group texts don’t use MUC. Rather, they use a special syntax in the JID, something like “+1XXX,+1YYY,…,+1ZZZ@cheogram.com”, where the + and , are required, the XXX, YYY, through ZZZ are the phone numbers (no dashes or other special chars just digits), and the @cheogram.com at the end is required.
I recommend the cheogram app if you’re on android. It has a lot of nice features on top of the Conversations base. I use gajim on my (linux) computer and it works well with jmp.chat.
I’m happy to answer other questions if you have them!
@New_scientist@feeds.twtxt.net No, Google does not predict this. “Google AI” has been self-promoting like this for decades. Remember when they used to brag that they could predict the onset of flu season weeks before it started? That silently went away because they got it badly wrong many times and people caught on to how bad their “predictions” actually were.
They can’t stop themselves. Anything about AI coming out of big tech companies these days is marketing, not real, and certainly not science.
I think I’m like a battery and I have maybe a hundred units of energy every day and every time I go up and down the stairs here one unit is drained from me.
here’s my old web page at Brandeis University
Coevolutionary algorithms typically explore domains in which no single evaluation function is present or known. For the purpose of selecting which individuals to maintain and vary, they instead rely on the outcomes of interactions between evolving entities.
I’ve been using variations of that same phrasing for a very long time–I wrote that web page circa 2005 maybe?
podman works with TLS. It does not have the "--docker" siwtch so you have to remove that and use the exact replacement commands that were in that github comment.
@prologic@twtxt.net hmm, bummer. I was hoping that translating the docker commands to podman syntax would work but it looks like it’s more subtle than that. Thanks for trying!
The weird thing was I wasn’t getting errors like that on my end when I tried it. podman thought the connection was created, and it set it as the default. But I don’t think it was sending anything over the wire. When I have more time to tinker with it maybe I’ll play around and see if I can figure out what’s up.
@prologic@twtxt.net I don’t get your objection. dockerd is 96M and has to run all the time. You can’t use docker without it running, so you have to count both. docker + dockerd is 131M, which is over 3x the size of podman. Plus you have this daemon running all the time, which eats system resources podman doesn’t use, and docker fucks with your network configuration right on install, which podman doesn’t do unless you tell it to.
That’s way fat as far as I’m concerned.
As far as corporate goes, podman is free and open source software, the end. docker is a company with a pricing model. It was founded as a startup, which suggests to me that, like almost all startups, they are seeking an exit and if they ever face troubles in generating that exit they’ll throw out all niceties and abuse their users (see Reddit, the drama with spyware in Audacity, 10,000 other examples). Sure you can use it free for many purposes, and the container bits are open source, but that doesn’t change that it’s always been a corporate entity, that they can change their policies at any time, that they can spy on you if they want, etc etc etc.
That’s way too corporate as far as I’m concerned.
I mean, all of this might not matter to you, and that’s fine! Nothing wrong with that. But you can’t have an alternate reality–these things I said are just facts. You can find them on Wikipedia or docker.com for that matter.
Solar Panel Placement
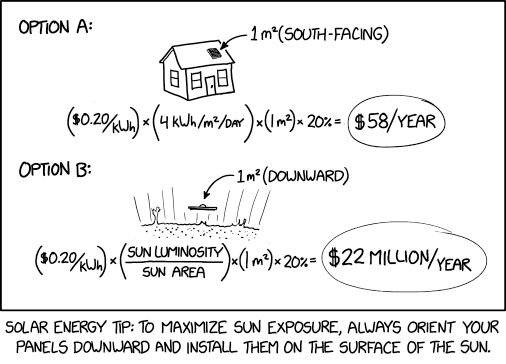 ⌘ Read more
⌘ Read more
@New_scientist@feeds.twtxt.net hello @prologic@twtxt.net here’s another feed that’s spewing multiple copies of the same post. This one above is repeated 8 times. @awesome-scala-weekly@feeds.twtxt.net now has 13 copies of each post every week. This definitely looks like a bug in whatever code is generating these feeds, because the source feeds don’t have multiple copies of the original posts:
- Has 8 copies of the above post: https://feeds.twtxt.net/New_scientist/twtxt.txt
- Has only 1 copy of the above post: https://www.newscientist.com/feed/home/
I forget whether I filed an issue on this before, but can you tell me where I should do that?
New kitchen time I think.
I’m playing around with snac2, which I think @stigatle@yarn.stigatle.no mentioned on here, and I have to say it’s extremely easy to set up and it’s been pretty straightforward so far. I wanted to experiment with having a presence on the Fediverse without going through the process of picking Mastodon vs. Gnu Social vs. Friendica vs. …, and I wanted to self-host instead of picking an instance of one of those. For now I’m abucci@buc.ci, but no guarantees that will remain stable; I’m just testing for the time being.